Now that the FCC has formally repealed its net neutrality guidelines, many net neutrality advocates are worried about how Internet Service Providers (ISPs) will respond. ISPs are middlemen who build and maintain the fiber optic cables and satellites that allow consumers to connect with Internet Content Producers (ICPs) like Facebook and Amazon. Net neutrality proponents worry that ISPs will create “fast” and “slow” lanes on the information superhighway, which would mean prioritizing some content over other content rather than handling it all in an equal fashion.
For instance, Netflix (an ICP) might pay Comcast (an ISP) to guarantee that Comcast customers can stream its movies at full HD resolution. Meanwhile, those who subscribe to Amazon Prime Video would have their internet connection throttled so that they could only stream in SD in order to avoid buffering issues. This would, of course, give Netflix a competitive advantage over Amazon but at the expense of users who would once have been able to watch either service at the same resolution. Without net neutrality, advocates worry that the internet will become a series of proprietary walled gardens rather than a digital commons where all users are treated fairly.
Yes, ISP Monopolies Are a Problem, but…
There are many reasons for skepticism about these fears. As others have noted, it is based on the popular misconception of the internet as a gigantic network of “dumb” pipes treating all data packets in an equivalent fashion, but net neutrality in a technical sense has not existed in decades. Services like video calls already receive privileged treatment over email and other less time-sensitive information. Furthermore, differential treatment of data is a vital precondition for innovation in online medical technology. Nobody wants the robo-surgeon—controlled by a doctor a thousand miles away—that is performing surgery on their body to suddenly be disrupted by a local user’s decision to torrent the latest season of Game of Thrones.
Even after “Ma Bell” was broken up, her child companies had what amounted to regional monopolies on telephone lines and, eventually, on access to the internet.
But net neutrality activists do have at least one legitimate concern. The post-net neutrality worst case scenario is made at least theoretically plausible because of the lack of competition between the handful of ISPs that dominate the market. As a legacy of the nearly century-long, State-protected Bell System telephone monopoly, even after “Ma Bell” was broken up in the 1980s her child companies had what amounted to regional monopolies on telephone lines and, thus, eventually, on access to the internet. Even today, the median American consumer has only a single ISP option for high-speed internet, if that.
The lack of competition among ISPs is a major problem and it is not hard to see how it could contribute to ISPs mistreating customers. After all, it is competition that forces companies in any industry to treat their customers fairly or else risk their customers choosing another provider. A lack of competition removes that natural, market-based disciplinary system. Given the lack of competition in many markets, the skepticism of pro-net neutrality activists towards the anti-competitive motives of the ISPs is not unwarranted.
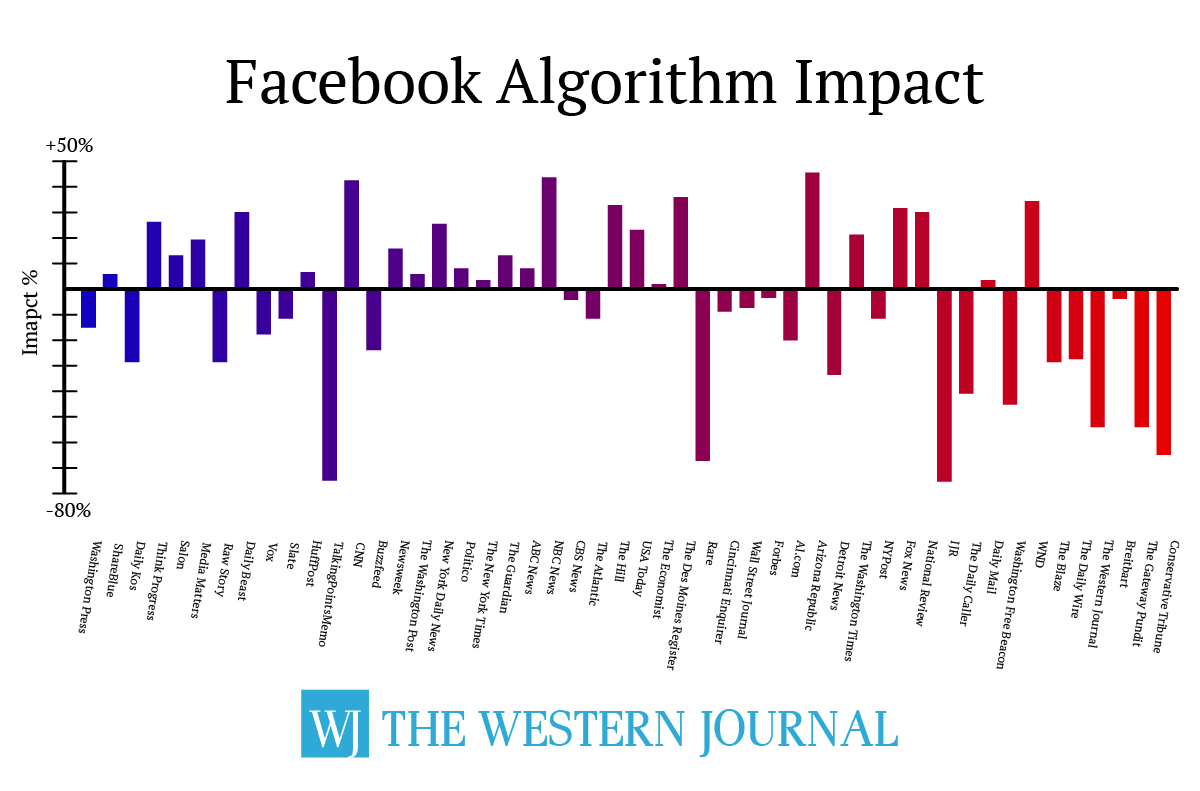
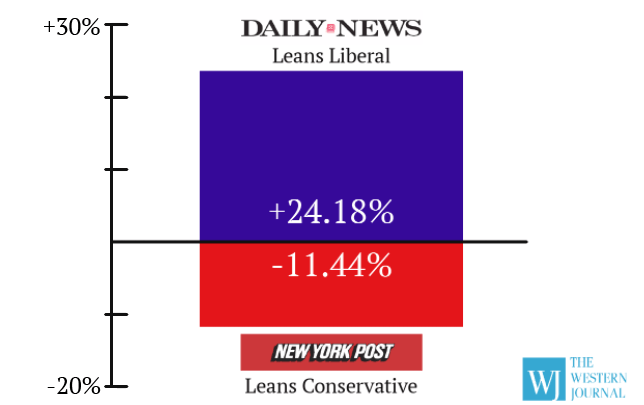
However, the same skepticism should be directed towards the major corporate sponsors of the pro-net neutrality push. As much as ISPs stand to gain from the end of net neutrality, Internet Content Providers (ICPs) stand to benefit from the rules remaining in place. This facet of the net neutrality debate remains under-examined.
Content Providers Have Everything to Gain
All of the major ICPs have backed net neutrality, including Facebook, Amazon, and Google. Each company has poured millions of dollars into the Internet Association, which lobbies Congress on their behalf. The organization backed a “Day of Action” in July 2017 in which members posted banner ads encouraging their users to protest the FCC’s rollback of net neutrality rules. Since then, the Internet Association has sponsored studies, successfully lobbied for the Senate to vote to preserve the rules, and sued to delay the rule change.
Wu’s suspicions ran directly counter to what these companies were actually doing at that very moment, which was opposing the repeal of net neutrality.
This has caused cognitive dissonance for some progressives in the tech sector who have traditionally framed the debate over net neutrality as a David-versus-Goliath struggle between activists and corporations. It is assumed that corporations have an inherent anti-competitive interest and so they will support regulatory policies that will allow them to extract “rent” from consumers. Since getting rid of net neutrality will allow these companies to extract larger rents, it is assumed that opposition to net neutrality would be the default corporate position.
Yet the most influential internet content providers—Alphabet (Google), Apple, and Amazon—all support net neutrality and each has a market cap several times larger than any of the major internet service providers. Clearly, there is no default corporate position on net neutrality. Instead, companies are generally divided on the issue along an ISP vs. ICP faultline.
Columbia Law School professor Tim Wu, who coined the term “net neutrality” in 2003, attempted to resolve this cognitive dissonance in an interview with Slate’s If Then podcast after the FCC’s decision to repeal net neutrality. One of the interviewers asked Wu whether he agreed that the end of net neutrality rules would “further entrench the power of these incumbents,” speaking of Facebook, Google, and Netflix. Wu noted that these companies once supported net neutrality but that now “everyone also knows that it’s to some degree to their advantage to climb up the ladder and pull it up after them.”
Of course, Wu’s suspicions ran directly counter to what these companies were actually doing at that very moment, which was opposing the repeal of net neutrality. How did Wu explain the dissonance between the actual actions of these companies and what “everyone knows” they really wanted to be doing? He said it was because their employees and consumers were pressuring them to support net neutrality even though they really wished they could stand against it. Wu concluded, “[Support for net neutrality] is against their philosophy, but not their business interests.” The interviewers quickly agreed. After all, it was something “everyone knows.”
Netflix Supports Net Neutrality Except When It Doesn’t
While nobody can definitively rule out the possibility that the likes of Google, Amazon, and Netflix formed a multi-million dollar lobbying outfit to push for the maintenance of net neutrality out of the fear of the ire of their users (and despite the prospect of reaping windfall profits from the repeal of the same), there is a much simpler explanation. Incumbent ICPs support net neutrality because they stand to benefit from the anti-competitive nature of the rules. We have been predisposed to think of net neutrality as a pro-competitive measure because we have only considered its effects on ISPs, but those rules also create an anti-competitive moat around market-dominate ICPs.
Consumers get better and cheaper access to content. The ISP gets paid. The market becomes more competitive.
Put yourself in Netflix’s position. As long as every entertainment streaming company is treated equally by the ISPs, Netflix can compete on its own terms: the impressive depth of its catalog and its ability to leverage its large user base in negotiating new content acquisition deals. But startup streaming companies compete on those terms at a severe disadvantage because by their nature they have neither many users nor much of a catalog.
Yet they might be able to compete with an incumbent like Netflix on access. Imagine a streaming startup paying a mobile ISP to give their service a “zero-rating” for their users, which means that the ISP would not count any mobile data used while streaming against the user’s data cap. In this scenario everyone, except for Netflix, wins. Consumers get better and cheaper access to content. The ISP gets paid. The market becomes more competitive.
While it may be true that “everyone knows” corporations have an anti-competitive interest, Netflix’s current anti-competitive interest is actually the use of net neutrality rules to prevent competition from insurgent ICPs. We do not have to rely on assumptions or hypotheticals to show this to be true.
Netflix was an incumbent in America but an insurgent in Australia, and it adjusted its position on net neutrality accordingly.
For example, while Netflix has long opposed zero-rating in America, where it is the market-dominant incumbent, it actually paid to have its service zero-rated when it launched in Australia in 2015. In the land “Down Under,” Netflix was an upstart, trying to compete with streaming services that had deeper catalogs of film and television made in Australia. If Netflix could not compete on catalog depth or user base, what could it compete on? Access.
Netflix paid an indeterminate sum to have the largest Australian ISP give its customers zero-rated access to Netflix. It may be fair to accuse Netflix of trans-Pacific hypocrisy, but it was responding rationally to its relative market position in both countries. Simply put, Netflix was an incumbent in America but an insurgent in Australia, and it adjusted its position on net neutrality accordingly.
Netflix is by no means the only ICP to have paid for zero-rating. Several times over the past decade, mobile ISPs have struck deals with ICPs to provide zero-rated streaming access. In 2012, Comcast zero-rated its own Xfinity video streaming service. More recently, there has been a flurry of similar deals as AT&T zero-rated HBO Now, T-Mobile did so for Netflix, and Verizon expanded access to its go90 service.
But What About the “Slow Lanes”?
It is no accident that this flurry of zero-rating happened in the immediate aftermath of the FCC’s announced repeal of net neutrality. One might wonder why net neutrality advocates would be so alarmed by the prospect of consumers receiving new, cheaper, and better service given that the ostensible goal of net neutrality is maximizing consumer internet access. But advocates reason that allowing ISPs to privilege one content provider over another would lead to “throttling,” in which the companies would create “slow lanes” for content from providers who did not pay for access to “fast lanes.”
The takeaway from Comcast’s throttling program should not be that ISPs wanted to end net neutrality for nefarious ends. Rather, it was much the opposite.
The most commonly cited example of throttling is Comcast’s campaign against BitTorrent users in 2007. This was during the height of the internet piracy boom when a relatively small number of users downloaded millions of illegally-shared music and video files. At the time, peer-to-peer (P2P) file sharing consumed between 49 and 95 percent of internet bandwidth (depending on the time of day), with most of that usage coming from fewer than 1 percent of internet users. A handful of P2P downloaders of movies, music, and porn were clogging up the internet for everybody else and disincentivizing investment in additional bandwidth.
Comcast wanted to make sure that the maximum amount of bandwidth was dedicated to serving the maximum number of users, but the FCC fined Comcast for doing so, stopping the throttling program as a violation of net neutrality principles. The takeaway from Comcast’s throttling program should not be that ISPs wanted to end net neutrality for nefarious, anti-competitive, and regressive ends. Rather, it was much the opposite. In 2007, net neutrality rules prevented Comcast from making changes that would have benefited 99 percent of users, incentivized investment in high-speed infrastructure, and created more competition between ISPs.
Fast forward to today when theoretical concerns about zero-rating have led net neutrality advocates to oppose giving actual users more and better access to content. What has happened since the FCC announced the repeal of net neutrality has not been Comcast-style throttling but the opposite, a kind of “widening” of the internet. Just as adding toll lanes to an actual highway can improve traffic speeds for all drivers while encouraging further investment in highway infrastructure, so too will adding high speed or zero-rated lanes to the internet superhighway.
To return to concerns about competition and net neutrality, advocates on both sides of the issue should devote at least as much attention to the anti-competitive motivations of the ICPs backing net neutrality as they do to the anti-competitive motivations of the ISPs which are opposed. In the end, consumers will benefit from an internet economy that maximizes robust competition between both content producers and service providers.
 Google is facing mounting pressure inside and outside the company over its plans for a censored search engine in China.
Google is facing mounting pressure inside and outside the company over its plans for a censored search engine in China.